MetaMask Issues Warning as Namecheap’s Hacker Send Phishing Emails

In a recent development, the renowned crypto wallet provider, MetaMask has issued a warning to investors over an anticipated hacking trap. The warning follows the phishing attempts made by Namecheap’s hackers to contact users through emails. On Sunday night, Namecheap found out that its third-party email system was being misused for sending unauthorized emails to MetaMask users. At the time, the firm explained the issue as an email gateway issue. Similarly, soon after identification, the system was stopped on an immediate basis.
We have evidence that the upstream system we use for sending emails is involved in the mailing of unsolicited emails to our clients. It was stopped immediately.
— Namecheap.com (@Namecheap) February 13, 2023
As the result of Namecheap’s breach, a big number of DHL and MetaMask phishing emails were sent to users to steal crypto wallet and their personal information. The phishing campaign began around 4:30 PM ET, and originated from SendGrit. Namecheap has been using the platform for an indefinite time, and is mainly used to send renewal notices. Furthermore, marketing emails of the firm are sent out using the same platform as well.
The Email read,
“We are writing to inform you that in order to continue using our wallet service, it is important to obtain KYC (Know Your Customer) verification. KYC verification helps us to ensure that we are providing our services to legitimate customers. By completing KYC verification, you will be able to securely store, withdraw, and transfer funds without any interruptions. It also helps us to protect you against financial fraud and other security threats. We urge you to complete KYC verification as soon as possible to avoid suspension of your wallet.”
MetaMask Faces an Uphill Task to Deal With Scam Emails
MetaMask took it to Twitter and talked about detailed measures users must take care of. The firm highlighted that it does not collect KYC information, and would not email users asking for their account information. Similarly, MetaMask made it clear that users must not enter their Secret Recovery Phrase on any website under no circumstances. In addition, others who might have received the email were asked to not click on any of the links and just ignore it.
Soon after the incident, Namecheap confirmed that its services were not breached, and no customer information was leaked. Within two hours, the firm completely restored its mail delivery systems. Namecheap is currently investigating the matter, and has suspended two-factor authentication and password reset services. The company stated,
“We would like to assure you that Namecheap’s own systems were not breached, and your products, accounts, and personal information remain secure.”
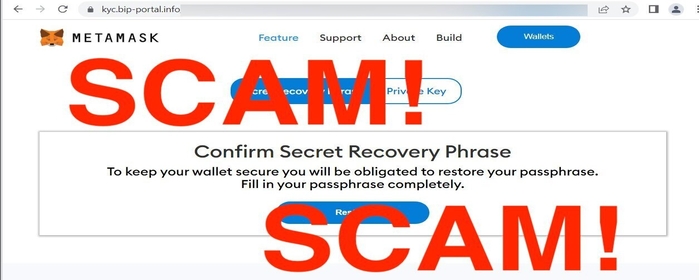
The phishing emails sent by scammers include a link that requests a Secret Recovery Phase on a fake MetaMask website. Similarly, the bogus page then imitates the users to enter private keys. The link redirects users to a phishing link. Once that’s done, these scammers import a user’s wallet on their devices, and flee with the funds and assets.
Keeping the incident in mind, a new scam, known as Address Poisoning, is on the rise. Under this situation, the hacker basically takes advantage of the carelessness of the user to drain all of their assets. The perpetrators send a transaction worth $0 to the wallets of the users whenever they conduct a transaction. At the same time, these hackers actively use a vanity address generator that generates an address almost identical to the address of a user.






