Phala Network – the First Confidential Network of Smart Contracts

Blockchain technology has shown lots of capabilities to us. The decentralization philosophy is no a myth anymore. Blockchains like Bitcoin and Ethereum have shown the potential for a fully decentralized system with full transparency. They make it possible for everyone to participate in the network and confirm transactions. But there are still some limitations to this system. Because everyone can join in the network, everything is visible for them.
As a result, businesses and individuals still don’t fully trust public blockchains. They can’t transact their confidential data on public blockchains. Phala Network is an answer for confidentiality in blockchains. It’s a Polkadot parachain with smart contract capabilities that guarantees the confidentiality of data.
Phala supports cross-chain and cross-contact interoperability. As a result, although data is confidential in Phala, smart contracts can interact with each other and other blockchains.
What is Phala Network?
The problem of privacy in public blockchains prevents many businesses and individuals from using them. They can’t trust a system with full transparency to store and transact their data.
Phala Network is a parachain on Polkadot working based on the PoS algorithm. It’s developed with a focus on solving the privacy issue in public blockchains and their smart contracts.
Phala Network plans to combine two features, privacy and confidentiality, and provide confidential smart contracts. Phala network will be a Polkadot parachain, thus benefiting from the natural security of that blockchain. It can provide the private smart contracts feature to other parachains, too. Current smart contract systems lack the combination of privacy and confidentiality. It’s the reason we see extensions like baseline projects emerge on Ethereum to give the needed features to businesses. After all, Phala can solve these challenges with its fundamental technology, TEE – Trusted Execution Environment.
TEE (Trusted Environment Execution)
TEE is the building block of Phala Network. It works as a layer over the system processor to isolate the running programs from other network components. The programs running in the TEE processor are somehow invisible to other parts of the system. All processes in the system need permissions to read data from TEE or write on it.
The protected area in the Phala processor still needs confirmation from blockchain validators. The beautiful fact is that TEE lets validators confirm the contracts, but the data is not visible to them.
Trusted Executed Environment is based on trusted hardware. Phala uses one of the most popular TEE systems, Intel SGX. Intel has developed a series of encrypting technologies in this system that makes it impossible for attackers to access the data inside. The state of smart contracts in the SGX system is unlike other public blockchains. It’s encrypted and sealed in SGX.
How Does Phala Work?
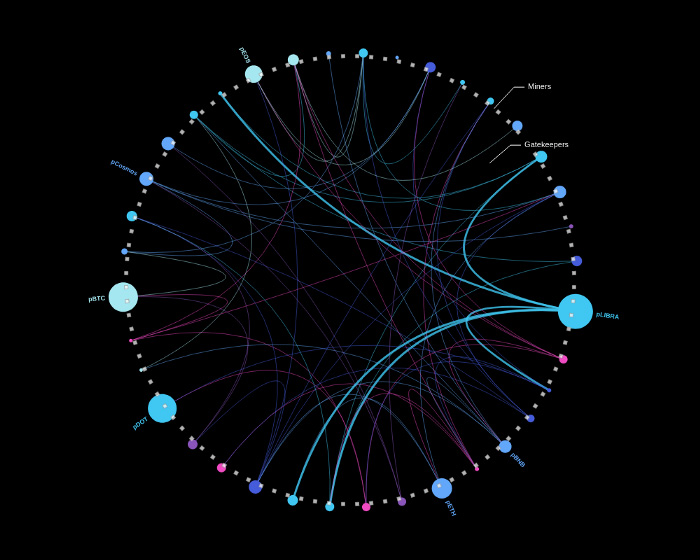
Three layers of operation and protection create Phala Network. Phala nodes, pRuntime, and Phost are the fundamental layers in Phala Network. pRuntime lives in TEE and therefore is protected from the outside world. Working on the TEE system is safe but still needs accurate programming and management to only allow valid transactions. Phost is the crucial player here.
Phost is the bridge between Phala blockchain and pRuntime. All the transactions need to pass phost to go to the pRuntime. Phala blockchain submits valis transactions, and they go to pRuntime – secured in TEE – through phost.
Miners and validators are active roles in the Phala Network. Although mining is entirely different in the Phala blockchain, it still needs special hardware for running Phala smart contracts. Phala miners should have a computer with TEE processors. They receive rewards for performing smart contracts in a secure environment.
Phala Network calls classical validators, Gatekeepers. Validators are crucial players in PoS blockchains. Gatekeepers not only validate block production in Phala Network but also stores special private keys. The blockchain uses these keys to decrypt smart contracts. As a result, miners don’t have access to smart contracts and their data. They just run the smart contracts, and Gatekeepers are responsible for decrypting the contracts.
As mentioned before, the Phala blockchain doesn’t run smart contracts. Miner with their TEE hardware run smart contracts, and the blockchain only ensures their availability. In other words, the blockchain manages the miners. If one miner goes offline, the Phala blockchain will replace them with other miners.
Phala Network is developed on Kusama, Polkadot’s canary network, for faster development. Kusama Dark Pool development kicked off in 2020 Q3, and the parachain launches on Kusama in 2021.
https://www.youtube.com/watch?v=EWOaIjN-FjI
Phala Products
Phala Network is a platform fur developing and running smart contracts. Decentralized applications can use this platform to serve users. There is an excellent potential for developing confidential applications on Phala. There are some applications currently running on this network. pLIBRA and Web3 Analytics are among the most popular ones.
pLIBRA
pLIBRA is an answer for the KYC challenge on Facebook’s Libra projects. It provides private transactions for Libra tokens. Besides, dApps running on Libra can use this product for a fully decentralized and private solution. Libra needs to implement KYC to answer the regulation worries. In other words, users have to provide their data to use Calibra wallet and Libra coin. pLibra makes it possible for them to provide their data, but the actual data will only be visible to the owner.
Web3 Analytics
Google Analytics is the most popular analytics solution for websites and applications. Web3 Analytics is the decentralized version of this program. Only if the service users give consent to use their data, the analytics program will collect and process their data about website visits and other actions. In other words, users have full control over their data. Something that isn’t possible yet in centralized systems.
Phala Network received a Web3 Foundation grant for both of the above products. It means the blockchain is on the correct path for becoming a successful parachain on Polkadot.
PHA – the Native Token of Phala Network
PHA is the primary token of Phala Network. It has many utilities, that most of them are focused on payments. Paying for CPU-time, on-chain storage, network bandwidth, and any other Phala resources is done by PHA token. Besides, it’s the native token for confidential smart contracts. Those contracts transact data and payments with PHA.
To become a Gatekeeper on the Phala network and guarantee the security of the system, you should stake a certain amount of PHA tokens. The tokens are locked to guarantee the goodwill and legal action of Gatekeepers. Besides, governing the blockchain is only available for PHA holders – with a certain amount of holding. Other use-cases include settlements for Phala products like Web3 Analytics and cross-chain bridges.
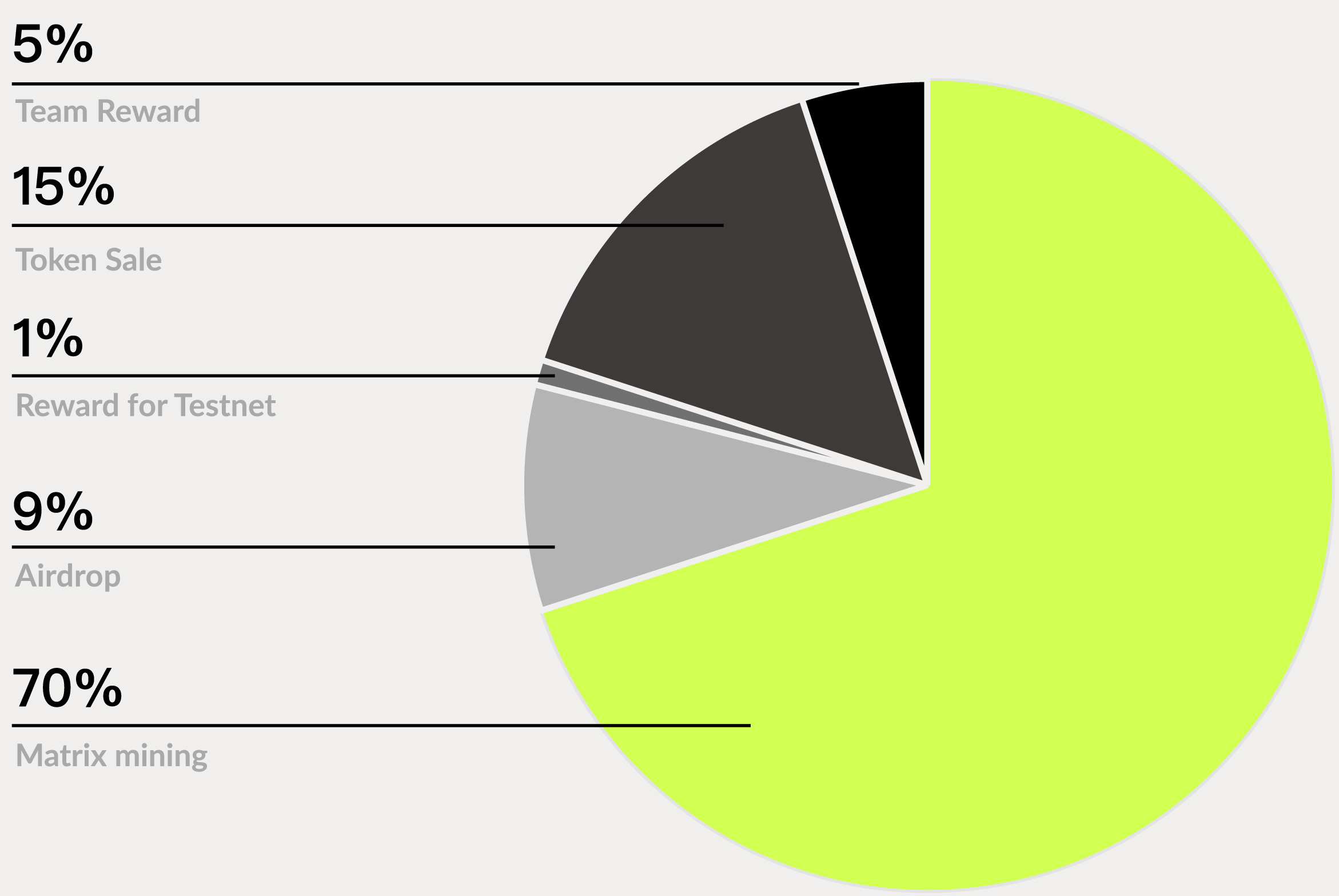
The distribution model for the PHA token is:
- 5%: Team Reward
- 15%: Token Sale
- 1%: Reward for Testnet
- 9%: Airdrop
- 70%: Matrix Mining – TEE miners
Users can receive PHA tokens in various ways. They can contribute TEE computing power and become miners. Being a Gatekeeper or Nominator is another way for getting PHA. for becoming a Gatekeeper, you need an Intel SGX-enabled computer with an ultra-fast network and enough power supply. For becoming a Nominator, you only need to hold PHA tokens.
Conclusion
Confidentiality has always been a significant burden in front of businesses that held them away from public blockchains. They needed some protected systems to hold and manage their data in a decentralized manner. Phala tries to solve this challenge with the help of TEE technology.
The blockchain uses the security levels of Polkadot for ensuring a safe environment, too. Some products are launched on Phala, and there are many opportunities for others looking for a confidential layer of security for their applications and transactions.
Phala Network Links
- Web: https://phala.network/
- Twitter: https://twitter.com/PhalaNetwork
- Medium: https://medium.com/phala-network
- Telegram: https://t.me/phalanetwork